OVERWATCH // ASM
AI-Powered Attack Surface Management
That Thinks Like a Security Analyst

A fully managed, AI-powered platform that continuously maps and monitors your entire external attack surface — and delivers clear, actionable intelligence straight to your dashboard.
Recon Phases
End-to-end reconnaissance pipeline that mirrors real attacker methodology—from discovery to validation—ensuring nothing is missed.
Recon Phases
Integrated tools working together in one platform to deliver clear, actionable intelligence.
Integrated Tools
Best-in-class security tools unified into a single workflow, eliminating tool sprawl and delivering correlated, actionable results.
Integrated Tools
Integrated tools working together in one platform to deliver clear, actionable intelligence.
AI Agents
Specialized AI agents working in parallel, each focused on discovery, analysis, prioritization, and reporting—like a full security team on demand.
AI Agents
Integrated tools working together in one platform to deliver clear, actionable intelligence.
AI Decision Points
AI-powered decision points analyzed in one platform to deliver clear, actionable intelligence
Your Attack Surface Is Growing Faster Than Your Organization Can Track
Organizations today have sprawling digital footprints — subdomains, cloud assets, exposed services, code repositories — and manual reconnaissance can't keep up.

Find it First
Exposed Assets
Misconfigurations
Vulnerabilities
Secure it Fast
Manual Recon Takes Weeks
Security teams spend 40+ hours per engagement running tools, correlating data, and writing reports by hand.

Find it First
Exposed Assets
Misconfigurations
Vulnerabilities
Secure it Fast
Manual Recon Takes Weeks
Security teams spend 40+ hours per engagement running tools, correlating data, and writing reports by hand.

Tool Sprawl & Data Silos
Analysts juggle 10–20 different tools with no unified workflow. Results live in scattered terminals and text files.

Tool Sprawl & Data Silos
Analysts juggle 10–20 different tools with no unified workflow. Results live in scattered terminals and text files.

ASM
Shodan
nmap
subfinder
Blind Spots Are Inevitable
Without comprehensive automation, shadow IT, forgotten subdomains, and exposed credentials go undetected.

ASM
Shodan
nmap
subfinder
Blind Spots Are Inevitable
Without comprehensive automation, shadow IT, forgotten subdomains, and exposed credentials go undetected.
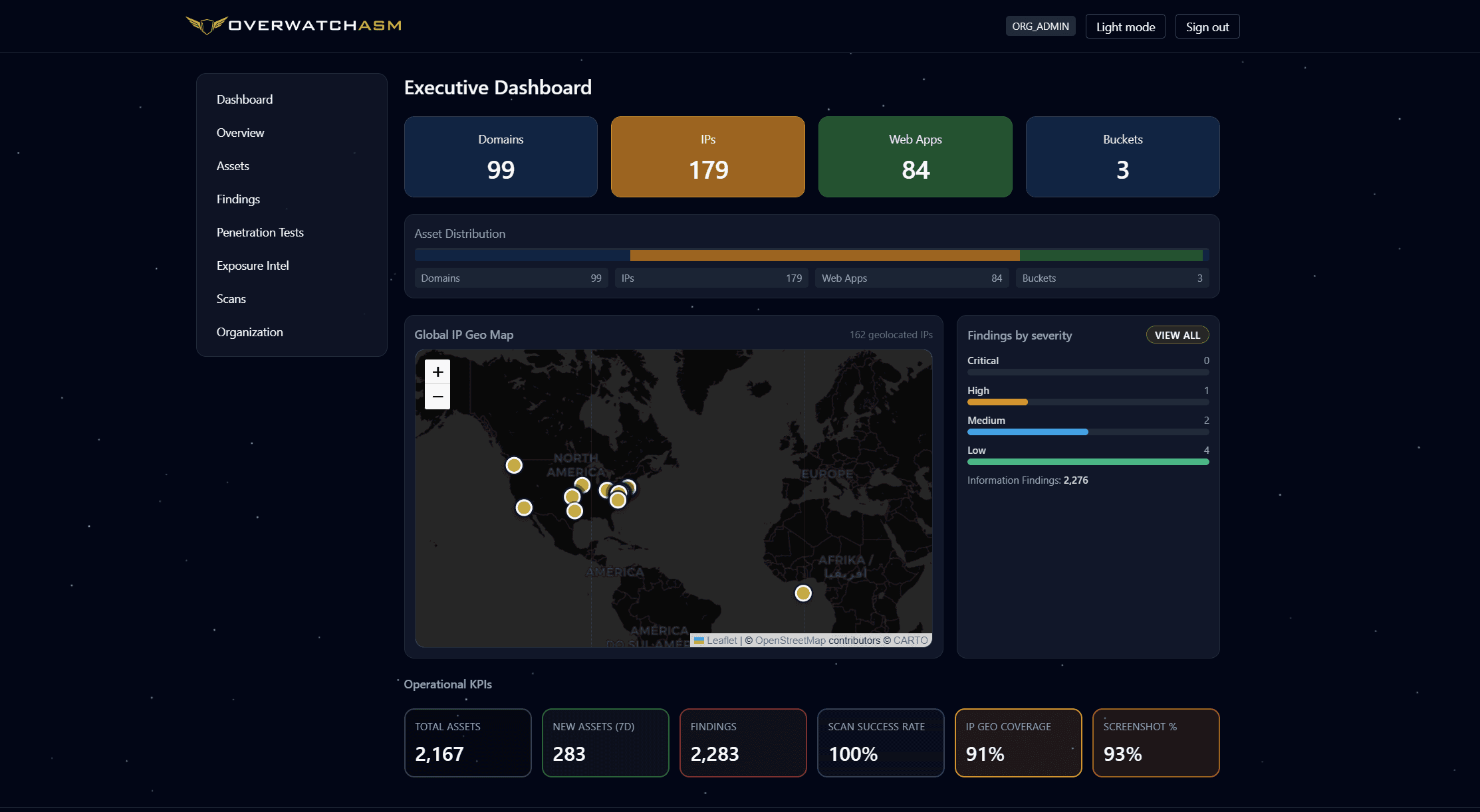
Everything OVERWATCH // ASM Discovers

Domains

Hosts

Certificates

Web Applications

Hosts

Cloud Buckets

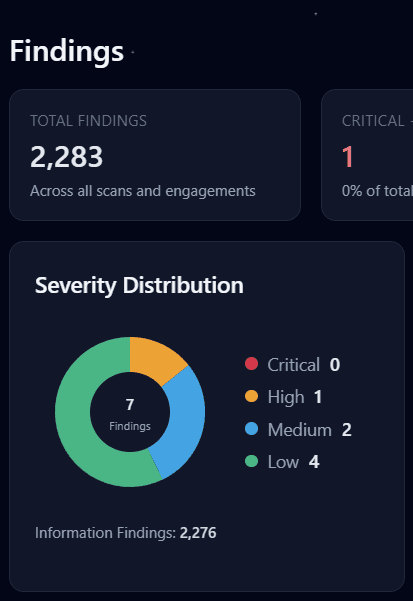
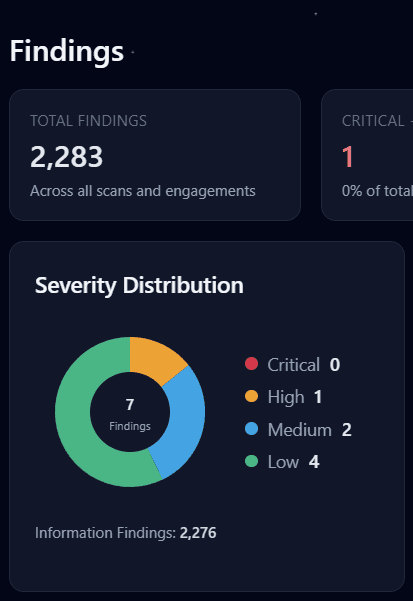
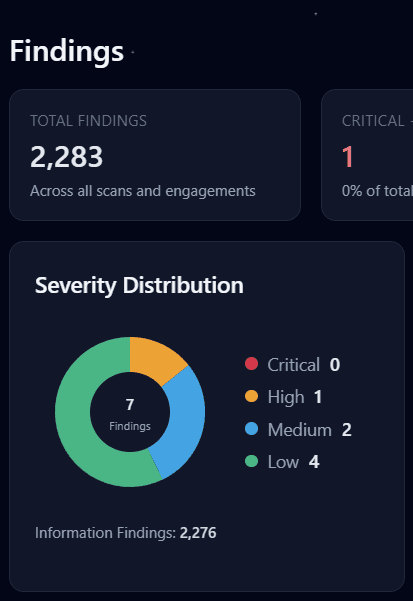
Vulnerabilities

Code Exposure

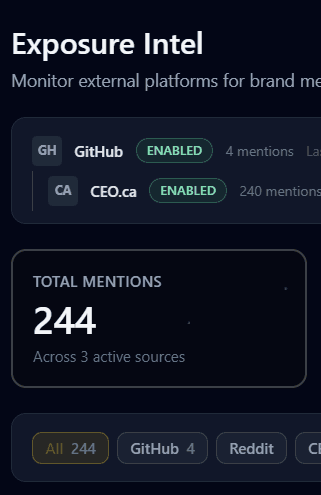
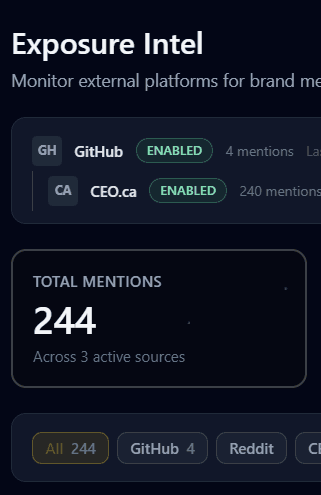
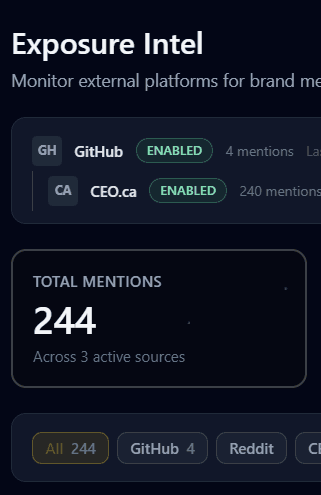
Exposure Intel

Subdomains

Domains

Hosts

Certificates

Web Applications

Hosts

Cloud Buckets
Vulnerabilities

Code Exposure

Exposure Intel

Subdomains
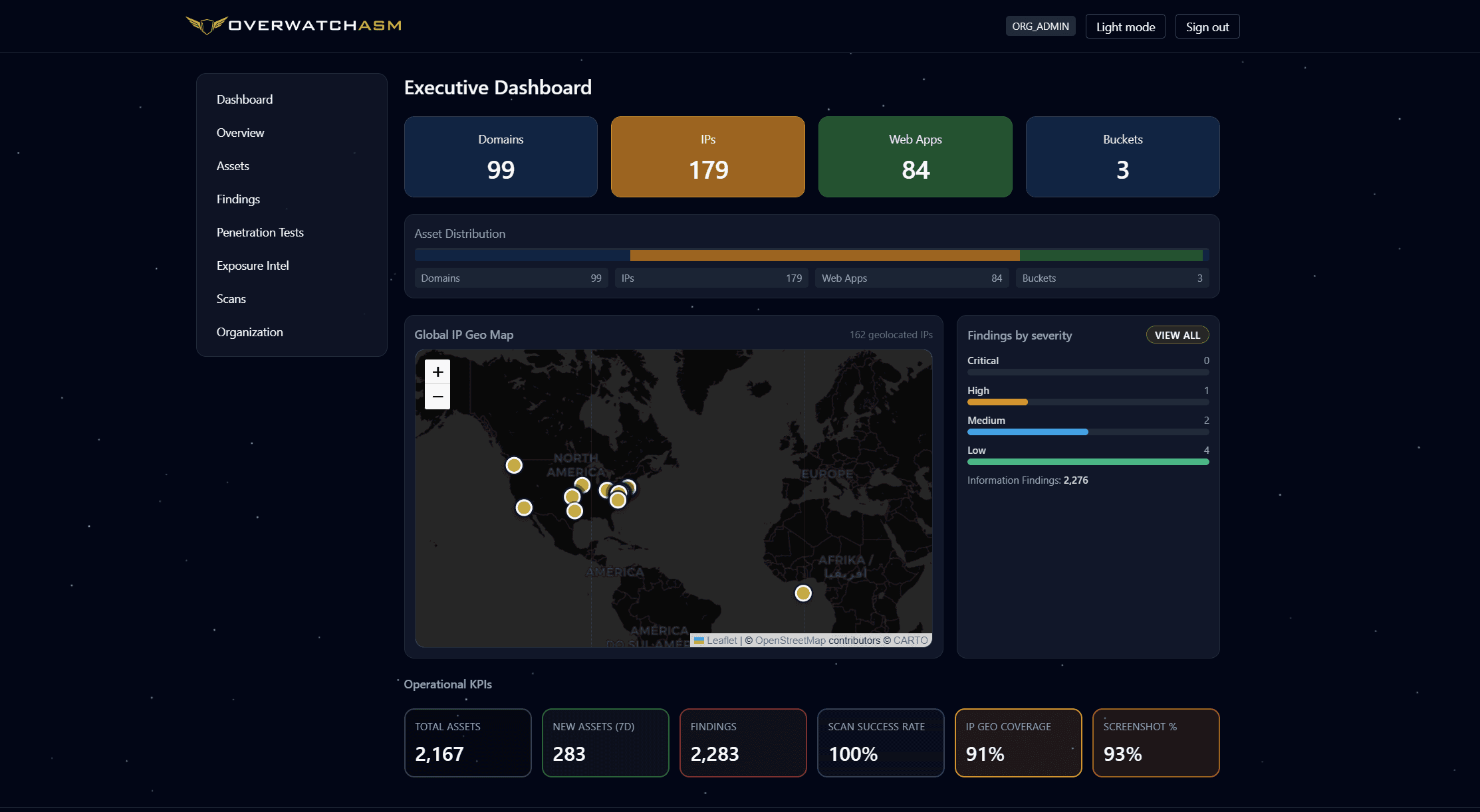
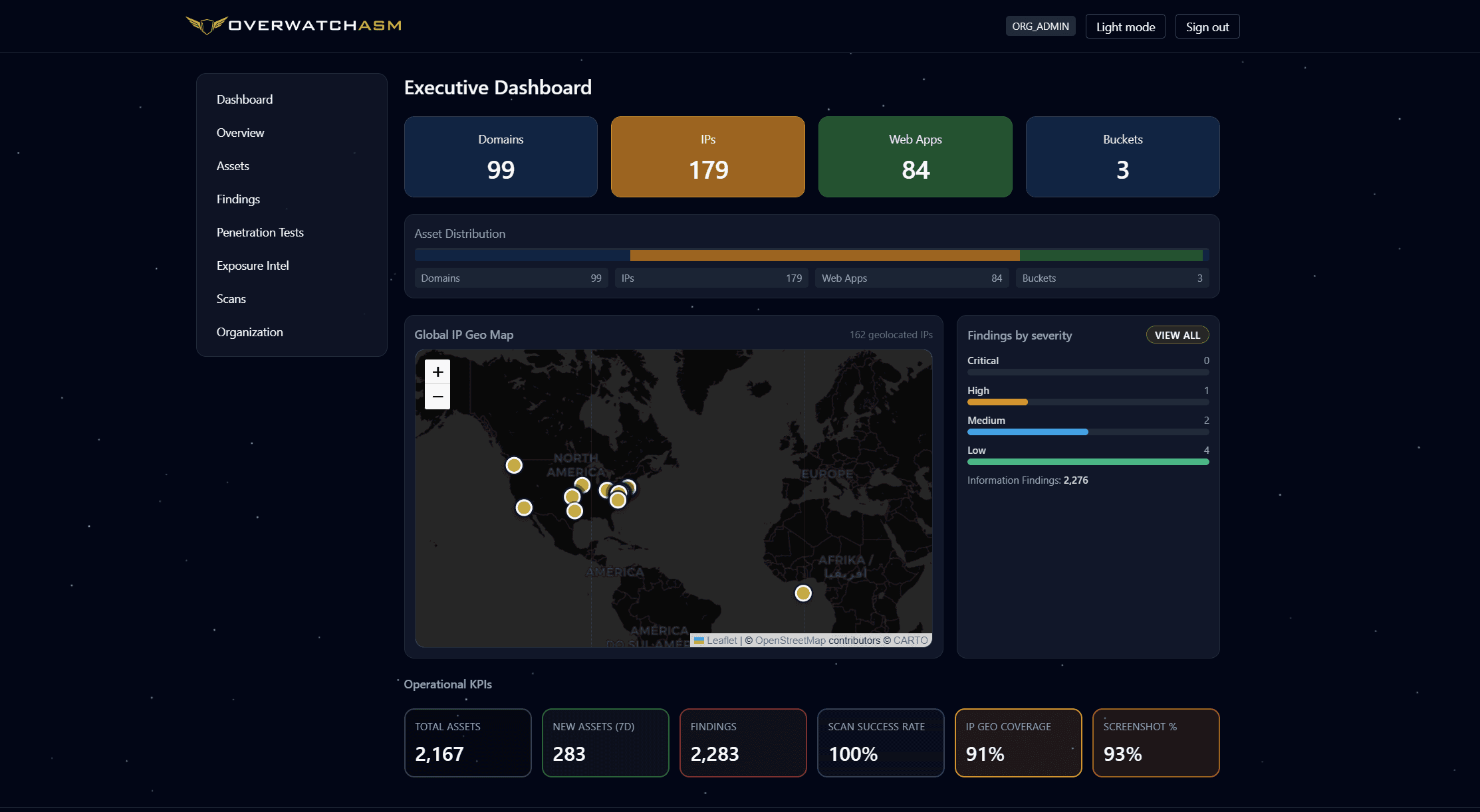
What Happens Behind the Scenes
When we run a scan on your behalf, eight specialized AI agents execute across six phases — mirroring how an expert analyst approaches recon, with AI judgment at every step.

PHASE 1 - Discovery

PHASE 2 - Profiling & Exposure

PHASE 3 - Proof Checking
PHASE 4 - Vuln Scan & Attribution

PHASE 5 - Risk Scoring

PHASE 6 - Reporting
Value for Every Stakeholder
Executives
Executives
Executives
Security Teams
Security Teams
Security Teams
Risk Teams
Risk Teams
Risk Teams


Fully managed recon.
Integrates with other tools and systems steamlining their worflow.


Fully managed recon.
Integrates with other tools and systems steamlining their worflow.


Fully managed recon.
Integrates with other tools and systems steamlining their worflow.

Discovery
Vulnerabilities
Risk Report
Profiling
AI analyst, not just automation.
Every decision — what to scan next, how to triage findings, what's a real risk — is made by LLM-powered reasoning, not static rules.

Discovery
Vulnerabilities
Risk Report
Profiling
AI analyst, not just automation.
Every decision — what to scan next, how to triage findings, what's a real risk — is made by LLM-powered reasoning, not static rules.

Discovery
Vulnerabilities
Risk Report
Profiling
AI analyst, not just automation.
Every decision — what to scan next, how to triage findings, what's a real risk — is made by LLM-powered reasoning, not static rules.

Executive-ready reports.
AI-generated reports with risk narratives written in plain language — ready to share with leadership, compliance, or your board.

Executive-ready reports.
AI-generated reports with risk narratives written in plain language — ready to share with leadership, compliance, or your board.

Executive-ready reports.
AI-generated reports with risk narratives written in plain language — ready to share with leadership, compliance, or your board.
Flexible pricing for every stage
60–90% less than competing platforms Compared to Censys ASM, CrowdStrike Falcon Surface, Palo Alto Expanse, and similar commercial solutions.

Starter
Small Business
$499
/per month
What’s Included:
Up to 3 root domains
1 organization
Monthly automated scans
AI-generated executive reports

Starter
Small Business
$499
/per month
What’s Included:
Up to 3 root domains
1 organization
Monthly automated scans
AI-generated executive reports

Starter
Small Business
$499
/per month
What’s Included:
Up to 3 root domains
1 organization
Monthly automated scans
AI-generated executive reports

Pro
Medium Business
$999
/per month
What’s Included:
Up to 15 root domains
5 organizations
Weekly automated scans
Priority support + onboarding

Pro
Medium Business
$999
/per month
What’s Included:
Up to 15 root domains
5 organizations
Weekly automated scans
Priority support + onboarding

Pro
Medium Business
$999
/per month
What’s Included:
Up to 15 root domains
5 organizations
Weekly automated scans
Priority support + onboarding

Enterprise
Large Business
What’s Included:
Unlimited root domains
Unlimited organizations
aily / on-demand scans
Full pipeline + custom agents

Enterprise
Large Business
What’s Included:
Unlimited root domains
Unlimited organizations
Daily / on-demand scans
Full pipeline + custom agents

Enterprise
Large Business
What’s Included:
Unlimited root domains
Unlimited organizations
aily / on-demand scans
Full pipeline + custom agents
Questions?
We're here to assist!
What does OVERWATCH // ASM actually do?
OVERWATCH // ASM continuously discovers, maps, and monitors your entire external attack surface—then delivers clear, actionable findings directly to your dashboard.
Can’t I just use AI tools like ChatGPT for this?
How quickly will I see results?
Do I need a security team to use this?
How is this different from a penetration test?
What does OVERWATCH // ASM actually do?
OVERWATCH // ASM continuously discovers, maps, and monitors your entire external attack surface—then delivers clear, actionable findings directly to your dashboard.
Can’t I just use AI tools like ChatGPT for this?
How quickly will I see results?
Do I need a security team to use this?
How is this different from a penetration test?
What does OVERWATCH // ASM actually do?
OVERWATCH // ASM continuously discovers, maps, and monitors your entire external attack surface—then delivers clear, actionable findings directly to your dashboard.
Can’t I just use AI tools like ChatGPT for this?
How quickly will I see results?
Do I need a security team to use this?
How is this different from a penetration test?
Know your exposure. Eliminate your risk.
See what attackers see—before they do.
Know your exposure. Eliminate your risk.
See what attackers see—before they do.
Know your exposure. Eliminate your risk.
See what attackers see—before they do.